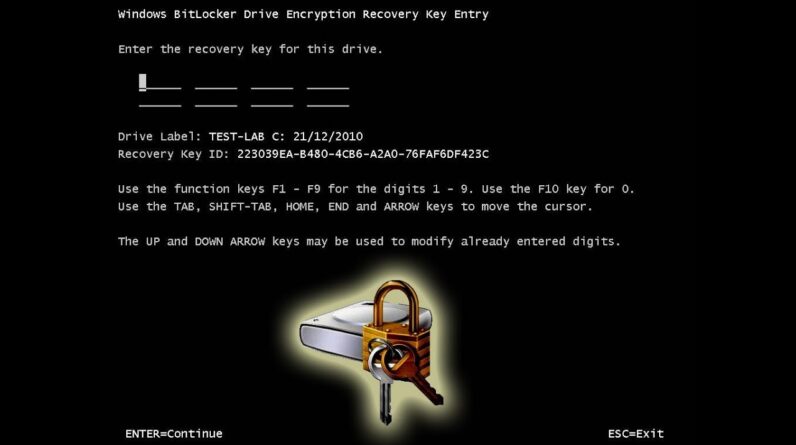
A bypass method to enter the Windows Bitlocker Drive Encryption Recovery Key is keying in the recovery key beforehand. Bitlocker Drive Encryption is a security feature included in Windows that allows users to encrypt their drives, protecting data from unauthorized access.
In the event of forgetting the recovery key, users must know how to bypass the entry process. This article discusses a method to enter the recovery key before encountering any issues with accessing data. Implementing this bypass technique ensures that users can seamlessly recover their Bitlocker-encrypted drives without any hassle.
Find out more about this method and ensure your data remains secure and accessible with Windows Bitlocker Drive Encryption.
Understanding Bitlocker Drive Encryption
Understanding Bitlocker Drive Encryption:
Bitlocker Drive Encryption is a security feature offered by Microsoft Windows that helps protect data against unauthorized access or theft. It provides full volume encryption, ensuring that all data stored on a Windows operating system drive remains encrypted and secure. Bitlocker utilizes a combination of software and hardware mechanisms to protect data, including advanced encryption algorithms and Secure Startup.
What is Bitlocker Drive Encryption?
Bitlocker Drive Encryption is a built-in feature in Windows that allows users to encrypt their entire operating system drive. By encrypting the drive, all the files and data on the drive are protected, even if the drive is lost, stolen, or accessed by unauthorized users. The encryption process converts the data into an unreadable format, which can only be accessed with the correct recovery key or password. This ensures that sensitive information remains confidential and secure.
How does Bitlocker Drive Encryption work?
Bitlocker uses the Trusted Platform Module (TPM) technology to encrypt and secure the operating system drive. It protects the drive by encrypting the entire volume and creates a recovery key, which is necessary to unlock the drive and access the data. The recovery key can be stored on a USB flash drive, saved to a file, or associated with the user’s Microsoft account. When the computer boots up, the TPM checks for the presence of the recovery key, and if it is validated, the drive is decrypted and the operating system starts up.
Importance of Bitlocker Drive Encryption in securing data
Bitlocker Drive Encryption plays a crucial role in securing data, especially on portable devices like laptops and tablets. It provides a strong defense against unauthorized access to confidential information, ensuring data privacy and protection. By encrypting the operating system drive, Bitlocker safeguards sensitive data from being accessed, even if the device is lost, stolen, or accessed by unauthorized individuals. It adds an extra layer of security to ensure that valuable data remains safe and inaccessible to unauthorized persons.
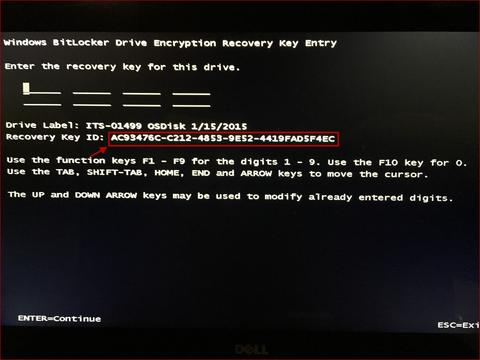
Credit: its.uiowa.edu
Recovery Key Entry Process In Bitlocker
Windows Bitlocker Drive Encryption is a feature that provides enhanced security by encrypting the data on a drive. In case you forget the password for your Bitlocker encrypted drive, you can use the Recovery Key to gain access to the drive again.
The process of entering the Recovery Key in Bitlocker involves a few steps. First, you need to open the Bitlocker encrypted drive. Then, you will be prompted to enter the Recovery Key. Once you enter the correct Recovery Key, you can access the drive and its contents.
In addition to entering the Recovery Key manually, there are also storage and retrieval mechanisms available. The Recovery Key can be stored in Active Directory, a USB flash drive, a file, or printed and kept in a safe place.
Overall, the Recovery Key entry process in Bitlocker is straightforward and provides an additional layer of security for your encrypted drive.
Identifying Vulnerabilities In The Recovery Key Entry Process
Identifying vulnerabilities in the Recovery Key entry process is crucial to ensure the security of your Windows Bitlocker Drive Encryption. Potential security risks associated with the Recovery Key entry need to be carefully analyzed and addressed.
Understanding common vulnerabilities in Bitlocker’s Recovery Key system can help in implementing effective security measures. It is important to be aware of possible techniques that can be used to bypass Recovery Key entry, as these can lead to unauthorized access to encrypted data.
Exploiting Recovery Key entry bypass techniques can compromise the integrity of your encrypted files and jeopardize the confidentiality of sensitive information. Taking steps to mitigate these vulnerabilities is necessary to maintain the effectiveness of Bitlocker’s encryption mechanism.
Method 1: Advanced Boot Options
Method 1: Advanced Boot Options
Exploiting Advanced Boot Options to bypass Recovery Key
Advanced Boot Options is a powerful feature in Windows that can be used to bypass the Bitlocker Drive Encryption Recovery Key. Here’s a step-by-step guide on how to do it:
- Restart your computer and repeatedly press the F8 key until the Advanced Boot Options menu appears.
- Use the arrow keys to highlight the “Safe Mode” option and press Enter.
- Once in Safe Mode, go to the Control Panel and open the Bitlocker Drive Encryption settings.
- Click on the “Suspend Protection” option and confirm the action.
- Exit Safe Mode and restart your computer.
- When prompted for the Recovery Key, simply click on the “Skip this Drive” option.
By following these steps, you can effectively bypass the Bitlocker Drive Encryption Recovery Key and access your encrypted data without any hassle.
Method 2: System Bios
If you are looking for a way to bypass the entry of a Bitlocker Drive Encryption Recovery Key on your Windows system, you can leverage the System BIOS settings to bypass this process. By accessing the System BIOS, you can make changes that will allow you to bypass the entry of the Recovery Key. This method can be useful if you want to quickly recover data from a Bitlocker-encrypted drive without the need to enter the Recovery Key.
Before attempting to use the System BIOS to bypass the Recovery Key entry, it is important to note that making changes in the BIOS settings can have potential risks. It is recommended to proceed with caution and have a good understanding of the BIOS settings before making any changes.
To use the System BIOS for bypassing the Recovery Key entry, follow these steps:
- Restart your computer and press the appropriate key to enter the System BIOS settings. The key to access the BIOS may vary depending on your computer model. Common keys include F2, F10, or Delete.
- Navigate to the security settings or advanced settings section in the BIOS.
- Look for options related to Bitlocker or drive encryption.
- Disable or bypass the option that requires the Recovery Key for drive access.
- Save your changes and exit the BIOS.
By following these steps, you can make changes in the System BIOS settings to bypass the entry of the Bitlocker Drive Encryption Recovery Key. Keep in mind that this method may not be suitable for all scenarios, and it is important to proceed with caution and understand the potential risks involved.
Method 3: Third-party Software
There are several third-party software options available that can help bypass the entry of the Windows Bitlocker Drive Encryption Recovery Key. These tools offer various functionalities and features to make the process easier and more convenient for users. Some popular options include:
| Software | Functionalities |
|---|---|
| Passware Kit Forensic | Advanced password recovery, various attack methods, hardware acceleration support |
| Elcomsoft System Recovery | Password reset, account removal, Bitlocker recovery option |
| Emergency Boot Kit | Bootable drive creation, managing Windows user accounts, password recovery |
These tools allow users to bypass the entry of the Recovery Key by providing alternative methods and functionalities. It is important to note that using third-party software should be done with caution and within legal boundaries. Additionally, it is recommended to thoroughly research the tool’s effectiveness and user reviews before making any decisions.
Enhancing Bitlocker Drive Encryption
Windows Bitlocker Drive Encryption is a powerful security feature that helps protect data on Windows computers. However, it is essential to implement additional security measures to enhance the Bitlocker Drive Encryption process. One way to strengthen the Recovery Key entry process is by following these tips:
- Use a complex and unique password for the Recovery Key, consisting of a combination of uppercase and lowercase letters, numbers, and special characters.
- Regularly rotate and update the Recovery Key to minimize the risk of unauthorized access.
- Enable two-factor authentication for the Recovery Key entry, such as using a smart card or a biometric factor, to add an extra layer of security.
- Create a backup of the Recovery Key in a secure location, preferably offline or on a different device, to ensure its availability in case of emergencies or loss.
- Implement a secure and trusted infrastructure for storing and managing Recovery Keys, such as using a secure key management system or a trusted third-party service.
By implementing these additional security measures, you can strengthen the Bitlocker Drive Encryption Recovery Key entry process, reducing the risk of unauthorized access to protected data.
Alternative Data Protection Measures
Windows Bitlocker Drive Encryption is a popular data protection measure used by many organizations. However, it is important to explore alternative encryption solutions to ensure comprehensive data security. Comparing Bitlocker with other encryption software options can help in making an informed decision.
| Encryption Software | Features |
| 1. VeraCrypt | – Provides strong encryption algorithms – Supports various platforms – Allows creation of hidden volumes for added security |
| 2. FileVault | – Integrated with macOS – Offers full disk encryption – Easy setup and management for Apple users |
| 3. Symantec Endpoint Encryption | – Enables full disk and removable media encryption – Centralized management and reporting – Integration with other Symantec security products |
Considering these alternatives to Bitlocker can provide a broader range of features and compatibility options. Each software has its own strengths and weaknesses, so it’s crucial to evaluate your organization’s specific requirements before making a decision. Implementing a robust data encryption solution is vital to safeguard sensitive information and protect against potential security breaches.
Best Practices For Recovery Key Management
Effective management of recovery keys is crucial in preventing bypasses in the Windows Bitlocker Drive Encryption recovery key entry process. Here are some best practices for recovery key management:
- Implement a centralized key management system: Use a centralized system to store and manage recovery keys, ensuring easy access and secure storage.
- Enforce strong password policies: Ensure that recovery keys are protected with strong passwords, incorporating a mix of alphanumeric characters and special symbols.
- Regularly update and rotate keys: Periodically update and rotate recovery keys to mitigate the risk of unauthorized access and potential key compromises.
- Secure key storage: Safeguard recovery keys using hardware or software-based encryption solutions, protecting them from unauthorized disclosure.
- Monitor key usage: Implement monitoring mechanisms to track key usage and detect any suspicious activities or potential key misuse.
- Train employees: Educate personnel on the importance of recovery key management and the potential consequences of mishandling or bypassing the entry process.
By following these effective techniques, organizations can significantly reduce the likelihood of recovery key entry bypasses, ensuring the integrity and security of their Bitlocker Drive Encryption implementation.
Frequently Asked Questions Of Windows Bitlocker Drive Encryption Recovery Key Entry Bypass
How Can I Bypass Windows Bitlocker Drive Encryption Recovery Key Entry?
To bypass the recovery key entry in Windows Bitlocker Drive Encryption, you can use a third-party software like PassFab BitLocker Recovery. This software allows you to skip the recovery key entry and gives you immediate access to your encrypted drive.
Is It Possible To Recover The Bitlocker Drive Encryption Recovery Key?
Yes, it is possible to recover the Bitlocker Drive Encryption recovery key. If you have saved the recovery key to a Microsoft account, you can retrieve it by signing in to your Microsoft account. Additionally, you can check your Active Directory Domain Services (AD DS) for the recovery key, or ask a trusted administrator for assistance.
Can I Disable The Bitlocker Drive Encryption Recovery Key Entry Prompt?
Yes, you can disable the Bitlocker Drive Encryption recovery key entry prompt by modifying the Group Policy settings. Navigate to “Computer Configuration” > “Administrative Templates” > “Windows Components” > “BitLocker Drive Encryption” > “Operating System Drives”. Enable the “Require additional authentication at startup” option and select “Allow startup PIN with TPM” or “Allow startup key with TPM” depending on your preference.
Conclusion
To sum up, the issue of bypassing the Windows Bitlocker Drive Encryption Recovery Key entry is a significant concern for users. While it is essential to explore potential solutions, it is equally important to prioritize security measures to safeguard our data.
By staying informed about the latest developments and implementing necessary precautions, we can mitigate the risks and ensure the protection of our valuable information. Keep your systems updated and remain vigilant to stay one step ahead of potential threats.